Bring True Autonomy to Access
Identity governance on auto-pilot. Balance ease of use with security. Ensure the right identities, both human and non-human, have the right access at the right time. No unauthorized access. No failed audits.







Dynamic Environments Demand Dynamic Access Governance
Leave behind rubber-stamping, audit risks or brittle workflows. Autonomous Identity Governance (IGA) turns intent into actions with the right explanation, keeps least-privilege intact, and closes audits fast.
Build a policy-ready identity foundation
Use Agentic AI to create clean RBAC/ABAC policies, unifying HRIS, IdP, apps, and usage data across human and non-human identities
Empower teams with access-ready decisions
Remove friction from granting access, boost innovation and agility, deflect IT tickets, and manual overhead.
Move fast while staying secure
AI suggests with clear evidence; you govern with SoD checks and closed-loop enforcement, weighing in where your judgement matters.
Solve Your Governance Use Cases
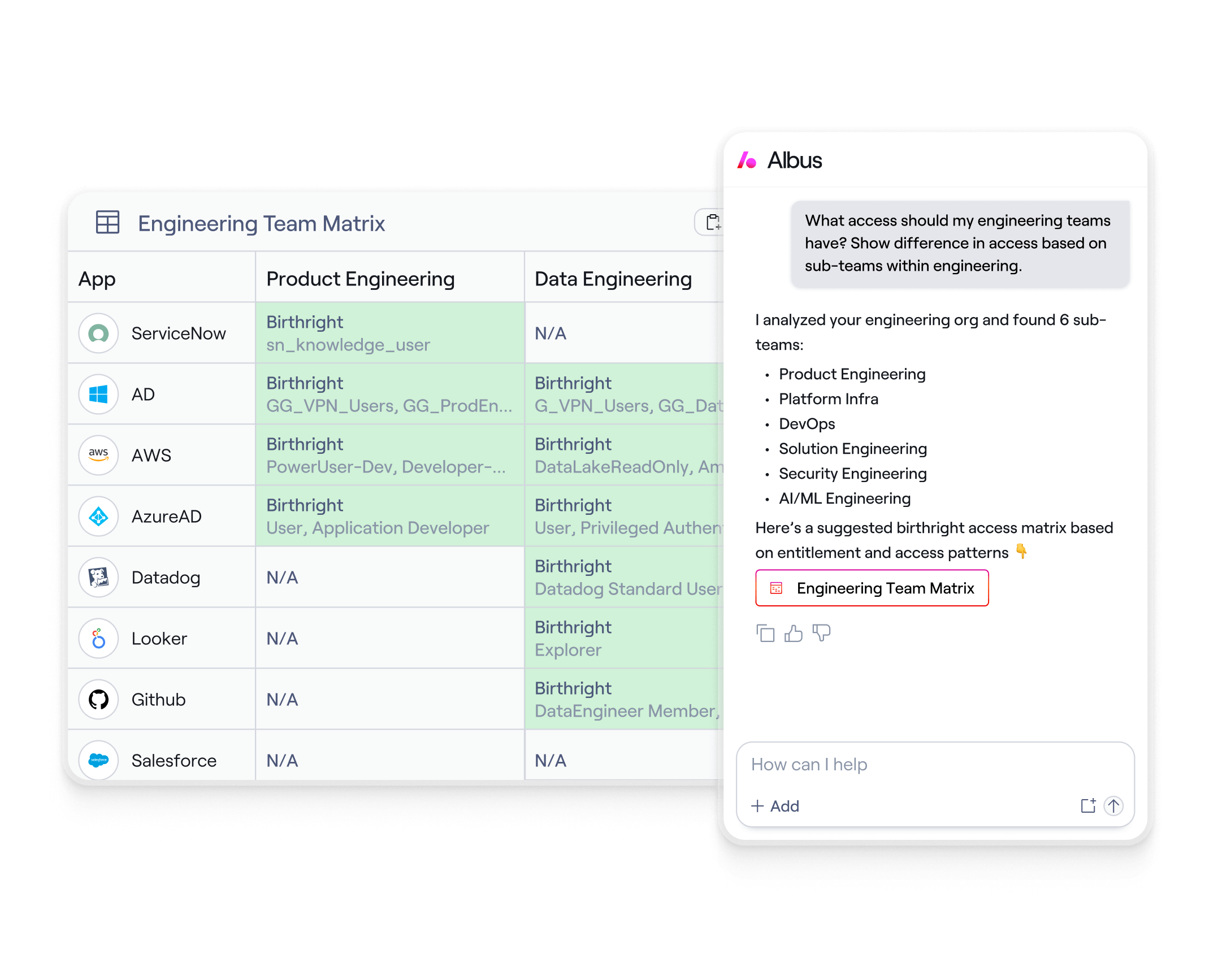
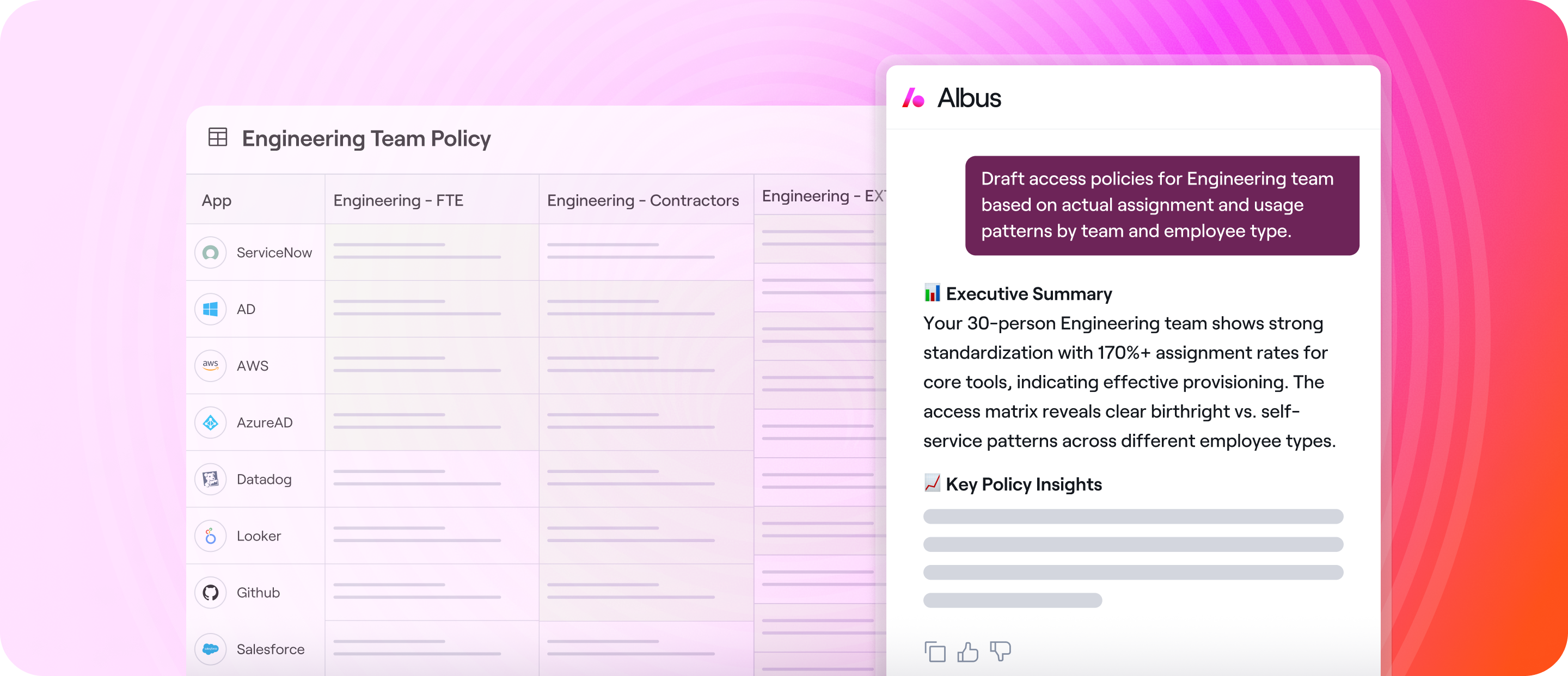
Architect clean access that keeps up
Use Albus to mine roles and draft RBAC/ABAC from key attributes and real usage. Policies adapt as orgs change, keeping least-privilege clean and current. Secure by design, scaled by AI.
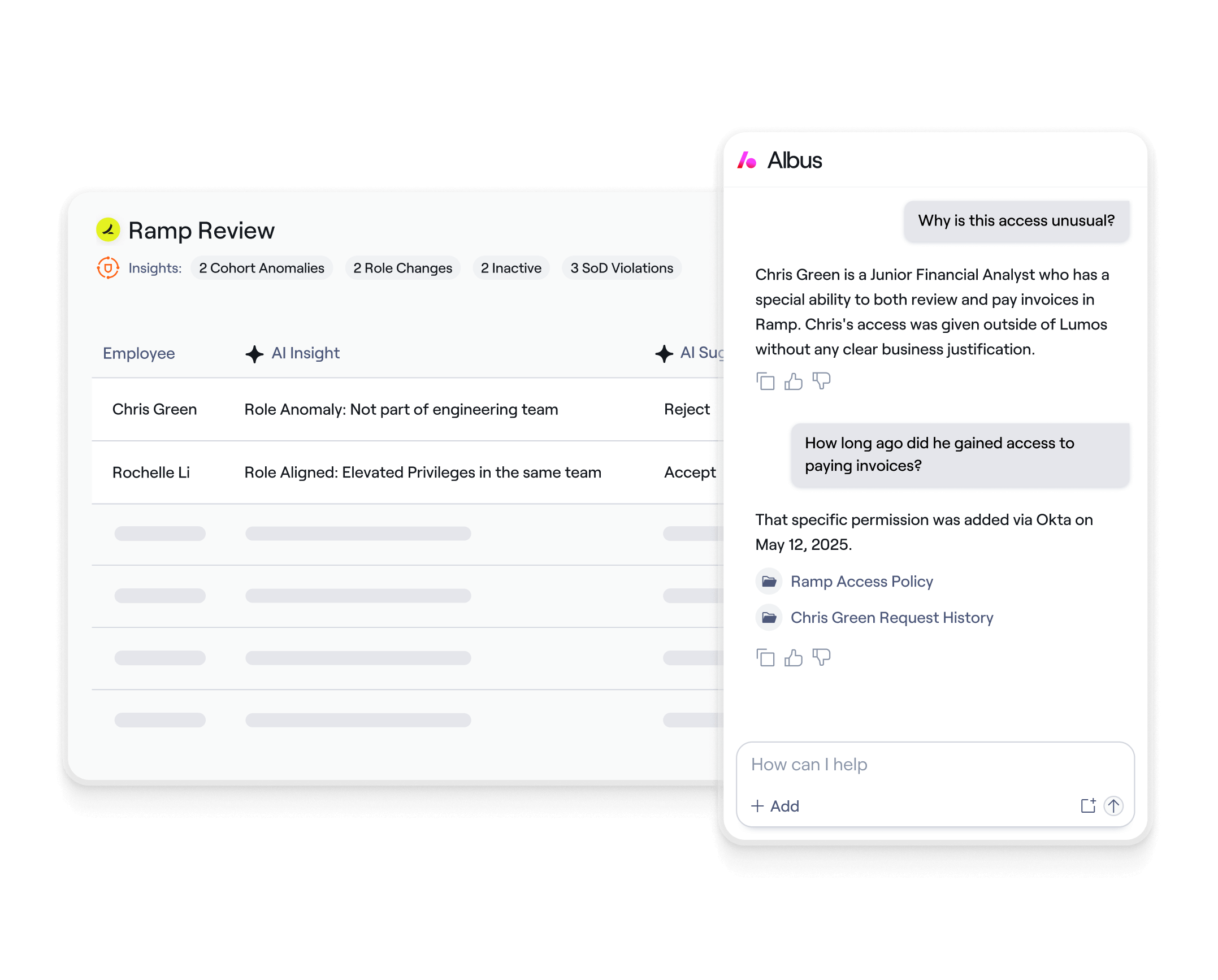
Deliver access reviews 7x faster
With Agentic UARs, run NHI and human access reviews in the same campaign, draft explainable decisions, and enforce remediation automatically. Finish reviews in minutes with audit-ready evidence.
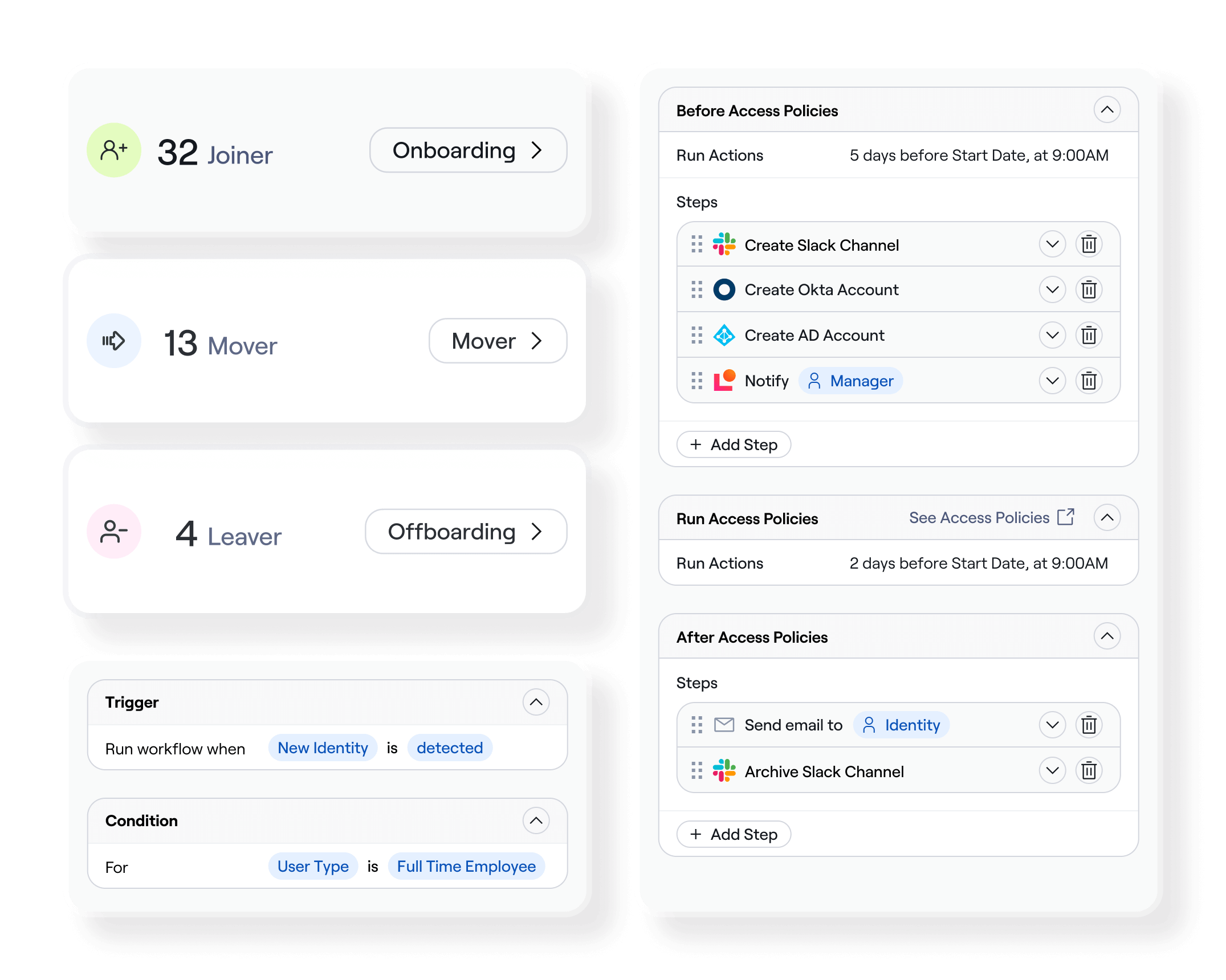
Automate to unlock productivity gains
Enable Joiner-Mover-Leaver workflows and Just-in-Time access so users get what they need in minutes, not days. Deflect tickets and free up IT for higher impact work. And when an employee leaves, Lumos can surface the service accounts and agent connections they owned, ensuring NHI access is reviewed alongside human off boarding.
Outcomes You Can Measure












Additional Resources
Frequently Asked Questions
Identity governance is the framework of policies, processes, and technologies that ensure the right individuals have the right access to the right resources at the right time. It helps organizations manage digital identities, enforce access controls, and maintain compliance. Lumos simplifies identity governance by automating user access reviews, provisioning workflows, and policy enforcement across your SaaS stack.
Identity governance and administration (IGA) is crucial for securing sensitive data, ensuring compliance with regulations like SOX and HIPAA, and reducing the risk of insider threats or privilege misuse. Without strong IGA, organizations face audit failures, overprovisioned accounts, and operational inefficiencies. Lumos addresses these challenges with an autonomous identity platform that enforces least-privilege access, automates lifecycle management, and provides real-time visibility into who has access to what; and why.
Key components of IGA include:
- Identity lifecycle management (Joiner-Mover-Leaver automation)
- Access certification and user access reviews (UARs)
- Role-based access controls (RBAC/ABAC)
- Policy enforcement and governance workflows
- Reporting and audit trails for compliance
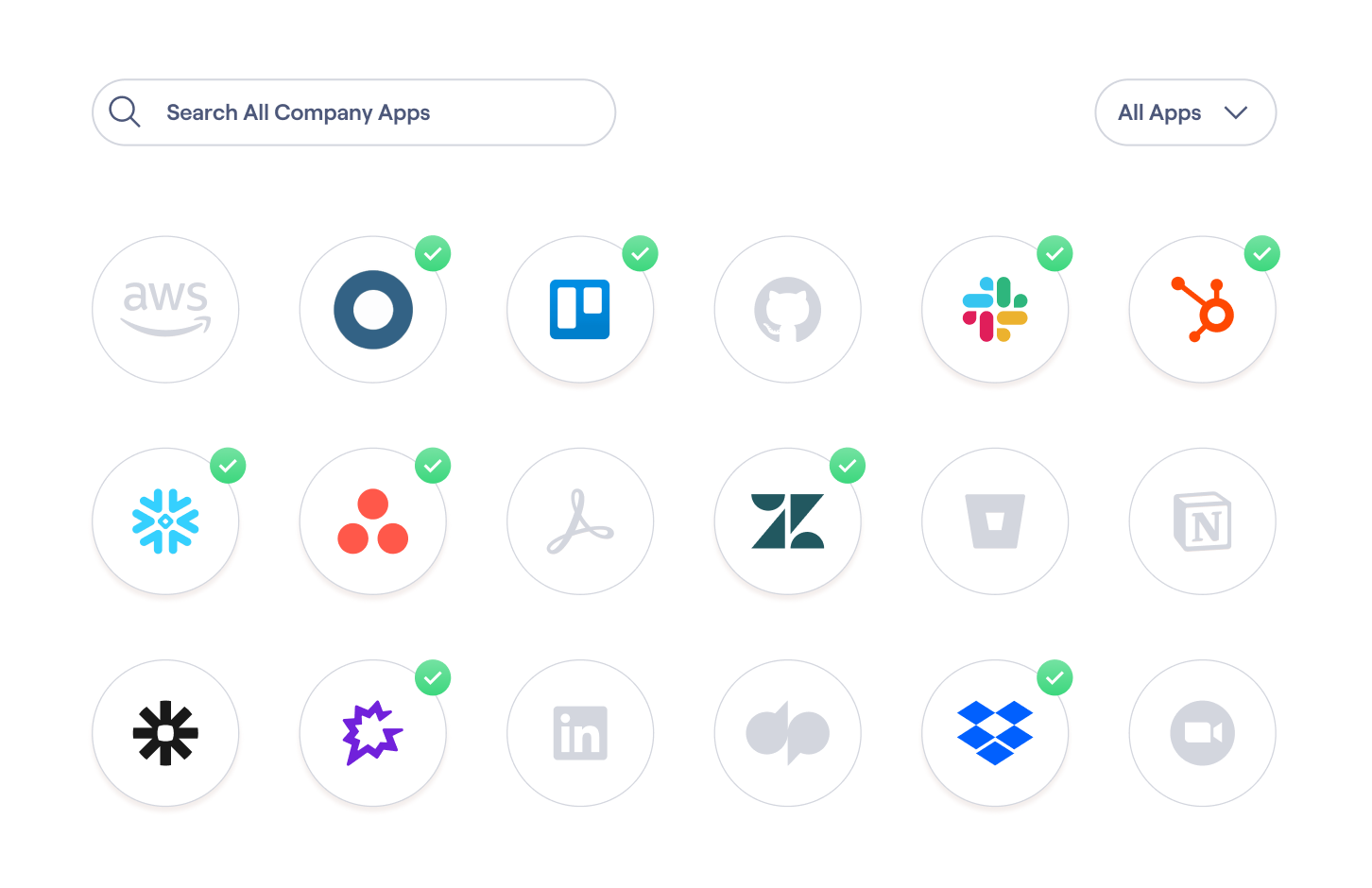
Lumos unifies all of these into a single platform, allowing organizations to automate and orchestrate identity governance across 300+ apps with AI-powered insights and Slack-native workflows.
An identity governance solution is a software platform that helps organizations manage user identities, control access to systems and data, and ensure regulatory compliance. It provides tools for automating access provisioning, conducting user access reviews, enforcing policies, and maintaining audit readiness. Lumos is a next-gen identity governance solution that accelerates deployment, reduces manual overhead, and secures both human and non-human identities – all with intuitive UX and out-of-the-box automation.
A common example of identity governance is automating user access reviews. Instead of relying on spreadsheets or manual ticketing, an identity governance platform like Lumos can schedule and run periodic reviews, notify app owners, log decisions, and enforce changes; all while maintaining audit trails. This reduces risk, ensures least-privilege access, and keeps your organization compliant.
The role of IGA is to ensure secure, compliant, and efficient access to resources across an organization. It enables IT and security teams to manage the entire identity lifecycle, enforce access policies, reduce overprovisioning, and streamline audits. With Lumos, the role of IGA expands: integrating automation, visibility, and AI into one unified platform that transforms identity governance from a manual chore into a strategic advantage.
Try Lumos Today
Book a 1:1 demo with us and enable your IT and Security teams to achieve more.



