Identity is at a Breaking Point
Feb 23, 2026
Manual identity governance can’t keep up with rising machine identities and evolving attacks. Discover why 2026 marks a turning point.
Last Updated
Apr 15, 2026

Stop. Take a second. Think about your organization and give yourself a quick, 1 to 5 rating on how prepared you feel to fend off an identity-based attack.
Do you have it in mind? Did you give yourself a 4 or a 5? Then you’re in the company of almost 92% of the organizations we surveyed for this year’s AI, Automation, and Risk report. That’s a lot of new friends! Grab a name tag, mingle, say hi to someone you don’t know yet, relax.
But also… don’t. No good thing can last forever, right? The reality is that of those same organizations we surveyed, only 3.8% made it through the last year without an identity-related security incident. MFA fatigue attacks, insider access, stolen and reused credentials; a whole host of identity-based attack vectors that let attackers into environments without ever needing to resort to detectable malware. They can just log in and use the access and tools you’ve already provisioned in their environment.
The reality of the new threat landscape is that identity has become a core driver for organizational security, at a time when the job of managing identities has become harder than ever.
Our research found several factors of the changing identity landscape that are contributing to the veritable canyon that exists between the sense of security and the actual number of orgs that made it through the year unscathed.
Why identity is getting harder to secure
Attackers have an increasing number of ways to simply log in
We all invest in tools and platforms to try to ensure that our company doesn’t become a headline, and we invest in those tools because they do make us safer; but the attacks themselves are changing. The sheer number of bad actors and the ease with which any ne’er-do-well with a keyboard and VPN can launch an attack mean that those defenses are sure to come up short somewhere. Attackers don’t need malware anymore, there are an increasing number of ways they can simply log in, and the shift towards those methods continues.
Because of those shifts, just 4% of companies made it through the last year without an identity-related security incident. Getting into the weeds of the numbers, nearly 65% of companies (64.6%, if you want to be exact, and I’m sure some of you do) saw three or more different kinds of identity-related incidents in the last 12 months. The top forms of incident were exploiting dormant access (which we defined as any account inactive for >90 days), MFA fatigue attacks, and insider access misuse.
As attackers continue to evolve the methods they use to access our environments, the numbers do show that leaders are thinking about and prioritizing the right areas of improvement. The most prevalent types of attacks do line up with the top concerns leaders have for their identity security. Excessive privilege accumulation, inability to detect misuse as it happens, and gaps in access reviews and stale entitlements were rated as the top three concerns, and those issues feed directly into dormant accounts hanging on past their expiration date, insider threats abusing overprivileged access, and excessive MFA requests going undetected.
There is a silver lining to this, though. Leaders are clearly thinking about and prioritizing the right improvements for their organizations. The unfortunate reality of the world we live in is that attacks and breaches are a matter of “when,” not “if,” but leaders are doing their best to prepare for that eventuality.
Machine identity is outpacing manageability
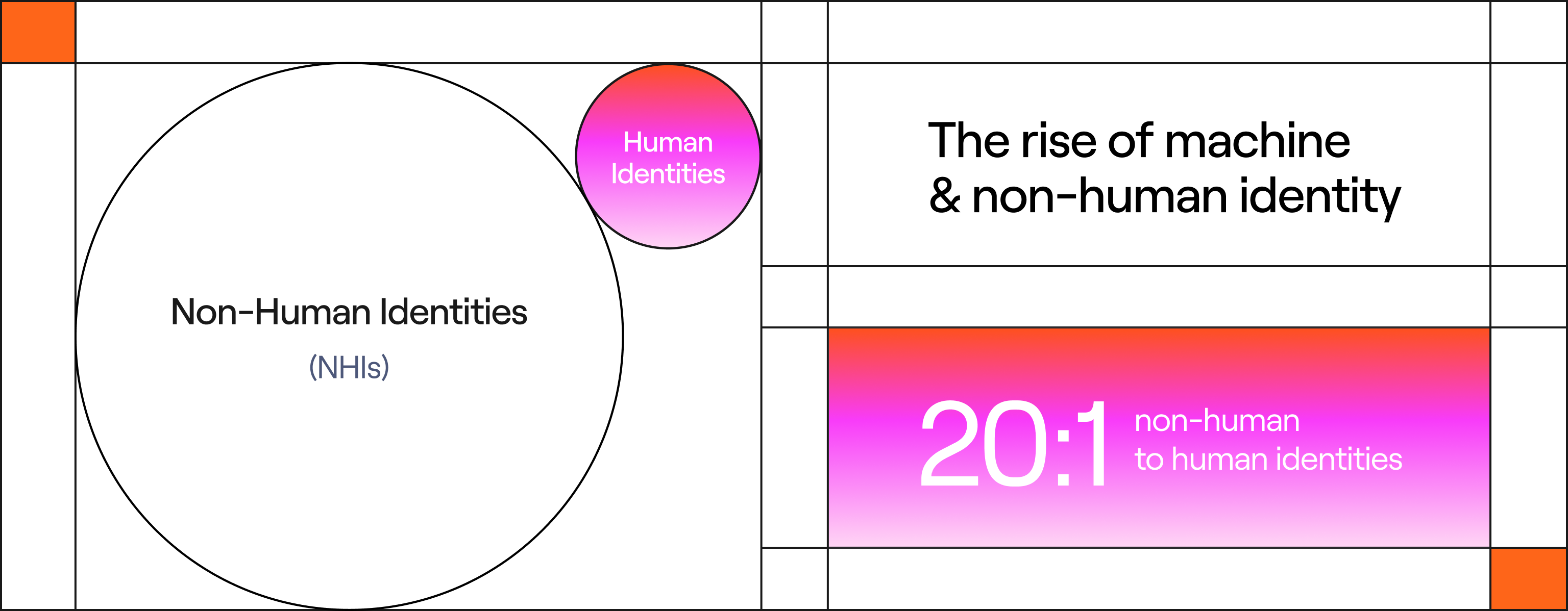
Machine identity, or non-human identity (NHI) as it’s also called, has been on the rise for a while. Headless servers and APIs and SaaS tools that required their own access were trending that line up and to the right, and then suddenly AI and agentic tools exploded onto the scene and sent that graph on an almost vertical trajectory. This explosion compounds the trends in attack methodologies, because more identities means an increase in the surface area attackers can try to exploit.
Most companies we surveyed still have more human identities than non, but the scales are already starting to shift to the other side. Of the organizations we surveyed, 46% already have at least one machine identity for every three humans, but that ratio crept as high as 20 machine identities for every human for forward-leaning companies. That’s an exponential growth, and it’s rapidly eclipsing organizations’ ability to manage. Only 35% of leaders said they’re very confident in their ability to govern and secure machine identity, a confidence level that makes sense in a world where every human you hire brings a potential 10x to 20x in workload.
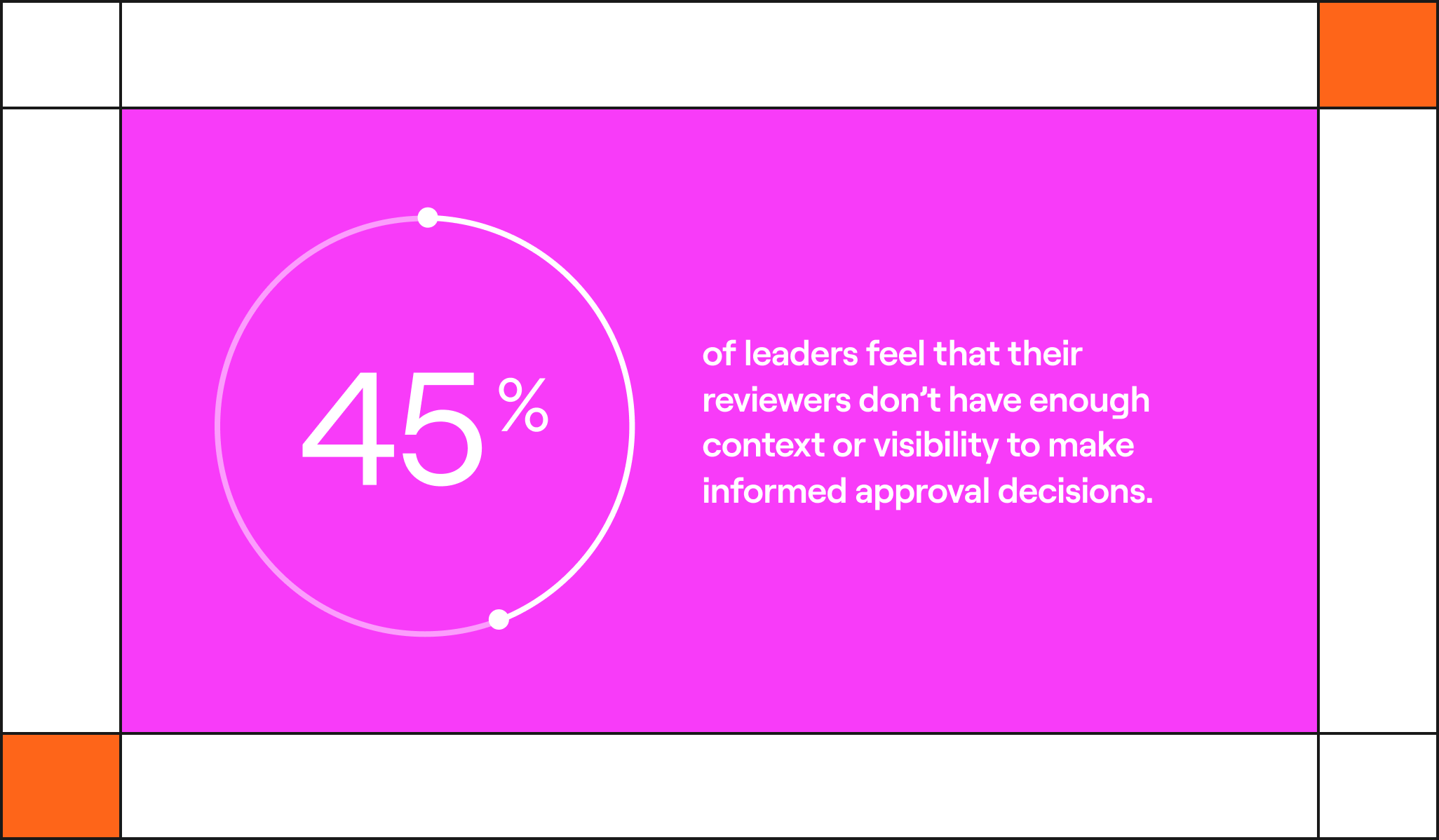
And as that number continues to explode, another statistic gives rise to concern: when it comes time to audit and approve existing access, for both machines and humans alike, 45% of leaders feel that their reviewers don’t have enough context or visibility to make informed approval decisions.
As machine identity will only continue to rise, leaders and reviewers will just become more mired in the backlog of analysis, rule-building, and tasks created by the expanding footprint, while simultaneously trying to stem the tide of attacks they’re facing. The situation is untenable, and leaders know they need help.
Leaders know they have to embrace AI and automation
Leaders can see that the landscape has changed and will continue to evolve rapidly, and they know they have to do something to meet that challenge. Almost every leader we surveyed, 88.7% to be precise, knows that AI and automation are a necessity to manage their identities and threats to them over the next 2 years. In fact, 85% of organizations have already started adopting AI as part of their identity security operations, albeit in very limited capacities. And therein, as the bard would say, is the rub.
While many organizations are dabbling with AI, almost none are utilizing its full potential to do heavy lifting. Only 4.5% of organizations currently trust AI to make even limited autonomous decisions. The issues we’re facing are already climbing faster than we can keep up, and in order to keep pace we, as a profession, need to be leveraging every advantage we can.
Fundamentally, the reason leaders aren’t using AI as much as they could, or perhaps should, is a lack of trust. The numbers clearly show that leaders want to embrace this tool, but most teams are only using AI to make recommendations or detections.
The hesitation expressed came down to a few key points.
First, most leaders feel there is a skills gap and lack of expertise. We’ve all heard endless talk of the cybersecurity skills gap for years, but in this case, where we’re talking about introducing a powerful tool to automate important tasks, that fear is understandable. Over 50% of teams expressed feeling unprepared to fully implement and utilize AI.
Over 50% of teams expressed feeling unprepared to fully implement and utilize AI.
The second reason many organizations aren’t using AI is that they simply don’t trust that the system will take the right actions. Fear of an AI breaking production with a rogue decision was expressed by 47% leaders who aren’t using AI, followed by fears of AI creating an even larger security hole.
Third, 46% of leaders feel that their technical debt needs to be sorted out before they hand the reins to an AI system. Messy data and inconsistent schemas cause chaos in their environment, as human operators try to make sense of tables and labels from different tools with overlapping definitions and use cases. There’s concern that implementing an AI tool on top of that existing chaos would lead to inconsistent results.
But all this hesitation stems from the idea of wholesale adoption on day one, and also ignores the strengths that AI presents. Fortunately, you don’t have to jump into the deep end on day one. The path to autonomous identity is a progression, not an all-or-nothing leap. By starting with high-impact use cases like AI-driven assessments to speed up stagnant User Access Reviews or identifying high-risk dormant accounts, teams can validate the AI’s reasoning and build the trust necessary for broader automation. Over time, as trust in the platform continues to grow, AI can transform your governance.
Close the gap today
It’s clear that the manual era of identity has reached its breaking point. With machine identity outnumbering humans 20 to 1 and adversaries moving at machine speed, the old ways of compliance-driven security is no longer enough to stay safe.
The AI, Automation, and Risk in 2026: Identity at a Breaking Point report goes into even more detail on the problems identity leaders are facing in their organization, breaks down the ways attackers are leveraging the existing gaps in identity security, and details concrete steps you can take to move your manual identity program into autonomous governance.
Are you ready to see the full roadmap for closing the gap and moving toward a state of actual, verifiable security? Read the report, and let’s talk.
Keep Reading
Try Lumos Today
Book a 1:1 demo with us and enable your IT and Security teams to achieve more.