JML Automation: Optimizing the Joiner-Mover-Leaver (JML) Process with Lumos
Aug 27, 2025
Learn how to automate the Joiner-Mover-Leaver (JML) process with Lumos to improve security, reduce IT tickets, and streamline onboarding and offboarding.
Last Updated
Oct 6, 2025

In modern organizations where employees join, shift roles, and eventually exit, the Joiner‑Mover‑Leaver (JML) process forms the backbone of identity lifecycle management. Automation of these transitions isn’t just a productivity booster—it’s a critical security control. According to CrowdStrike’s 2025 Global Threat Report, an overwhelming 80% of cyberattacks leverage identity-based methods. This data underscores the urgent need for efficient JML management.
JML automation streamlines provisioning during onboarding, adjusts access for internal role changes, and ensures prompt deprovisioning when employees depart. By orchestrating these workflows through identity governance and access management tools, organizations reduce manual errors, enforce least-privilege access, and maintain strong security postures.
This article delves into how JML automation works, why it matters, and how it fits into broader identity lifecycle strategies to strengthen compliance, efficiency, and risk mitigation efforts.
What Is the Joiner-Mover-Leaver (JML) Process?
Despite its importance, many organizations still manage JML manually through IT tickets, spreadsheets, and ad hoc workflows. This creates several persistent challenges:
- Ticket Sprawl: Every onboarding, role change, or departure generates multiple IT tickets, overwhelming service desks and delaying responses.
- Delayed Onboarding: New hires often wait days or weeks for full access, reducing productivity and creating poor first impressions.
- Slow Revocations: Departing employees may retain access for days after leaving, introducing serious security risks such as insider threats or account misuse.
This manual approach is time-consuming, error-prone, and costly.
Lumos eliminates these repetitive requests through full-cycle, policy-based automation. By defining rules for access based on role, department, or seniority, Lumos automatically provisions accounts for joiners, updates entitlements for movers, and revokes access for leavers in real time. This not only improves operational efficiency but also strengthens security and ensures compliance with regulations.
With Lumos, IT and security teams can move from reactive ticket handling to a strategic, automated JML framework that scales with the business.
Why Automating the JML Process Is a Business Imperative
Managing identity through the Joiner-Mover-Leaver (JML) lifecycle is no longer a back-office function; it’s a strategic necessity. In a world of hybrid work, constant organizational change, and rising cyber threats, automating JML workflows is critical for protecting sensitive data, maintaining operational agility, and ensuring compliance. Manual processes not only create inefficiencies but also introduce risk. Lumos solves this by delivering real-time, policy-driven JML automation at scale.
Rising Complexity in Hybrid and Remote Work Environments
Today’s workforce is fluid. Employees join, switch teams, and leave more frequently than ever – while working across dozens (or hundreds) of distributed SaaS and on-prem tools. Traditional JML processes, which rely on IT ticket queues and manual coordination, simply can’t keep up.
Lumos eliminates these bottlenecks by integrating directly with your HRIS and Identity Provider (IdP). Any update, like a role change or termination, triggers an automated workflow that provisions, modifies, or revokes access across 300+ integrated applications and custom applications across cloud and on-premise environments. Whether an employee joins from finance or moves into engineering, Lumos automatically adjusts entitlements based on real-time data and predefined policies: no tickets or delays.
Security Risks of Manual JML Handling
Manual JML processes leave too much to chance. Delays in offboarding can leave former employees with lingering access to critical systems, increasing the risk of insider threats and compliance violations. Similarly, unadjusted access during role changes can result in privilege creep and expanded attack surfaces.
With Lumos, offboarding is immediate and complete. As soon as a termination event is detected, Lumos deprovisions access based on role, department, or custom logic – ensuring that every account is closed and every permission revoked. This reduces security exposure and strengthens least privilege enforcement across the organization.
Compliance Pressures
Regulatory frameworks like GDPR, HIPAA, and SOX require strict controls over access to sensitive data; and evidence to back it up. Manual JML workflows make it difficult to prove compliance without exhaustive documentation and time-consuming audits.
Lumos builds audit readiness into the JML process. It supports time-bound access, activity logging, and just-in-time provisioning, providing clear records of who had access, when, and why. Risk and compliance teams gain the visibility they need, while IT automates the governance controls auditors expect.
In short: JML automation with Lumos isn’t just about efficiency – it’s essential for security, compliance, and scale.
Key Benefits of Automating JML Workflows
When the JML process is automated, organizations unlock more than just convenience: they gain security, efficiency, and strategic control. From reducing risk to improving employee onboarding, automated JML workflows can dramatically enhance how IT and security teams manage identity at scale. Lumos brings these benefits to life through a unified platform built to streamline the entire identity lifecycle.
- Enhanced Security Through Timely Access Management
- Improved Operational Efficiency and Cost Savings
- Real-Time Visibility and Activity Monitoring
- Improved User Experience and Talent Retention
- Support for Data-Driven Decision Making
Enhanced Security Through Timely Access Management
Security begins with access hygiene. Lumos ensures that permissions are automatically assigned – and revoked – based on role, department, and real-time HRIS or IdP signals. This eliminates the delays and inconsistencies of manual processes, reducing the risk of overprovisioning and privilege creep. With Lumos, least privilege is enforced by default, closing security gaps before they can be exploited.
Improved Operational Efficiency and Cost Savings
Automating JML doesn’t just make processes faster; it frees up valuable IT bandwidth. Lumos eliminates the need for repetitive JIRA tickets and manual follow-ups, reducing the volume of access-related tasks. Organizations using Lumos have reported saving hours per employee during onboarding and offboarding, allowing IT to focus on higher-value work and reducing operational costs across the board.
Real-Time Visibility and Activity Monitoring
With Lumos, IT and security teams get a complete view of who has access to what, why they have it, and for how long. This visibility spans all apps – cloud and on-prem – and includes privileged, temporary, and exception-based access. Whether you're conducting an audit or reviewing usage patterns, Lumos delivers clear, centralized access intelligence.
Improved User Experience and Talent Retention
Nothing frustrates new employees like waiting days to get the tools they need. Lumos solves this with persona-based, automated access bundles that deliver the right tools on day one: no tickets, no delays. This smooth start boosts satisfaction, reduces friction, and supports long-term employee engagement and retention.
Support for Data-Driven Decision Making
With Albus, Lumos’ AI identity agent, organizations gain deep insights into access behaviors, anomalies, and policy effectiveness. Albus helps identify underused permissions, misaligned roles, and optimization opportunities; enabling continuous improvement of access governance and policy enforcement.
Lumos turns JML automation into a strategic asset: supporting scale, security, and smarter decision-making.
Breaking Down the JML Phases with Automation
The Joiner-Mover-Leaver lifecycle doesn’t have to be manual, fragmented, or ticket-driven. With Lumos, each phase of the identity lifecycle – from day-one onboarding to final offboarding – is orchestrated through automation, delivering consistency, speed, and security at scale. Here's how Lumos breaks down and streamlines each phase of JML with purpose-built workflows.
- Streamlined Onboarding
- Role Changes and Access Adjustments
- Fast, Secure Offboarding
Automating the Joiner Phase: Streamlined Onboarding
First impressions matter; especially in IT. Lumos ensures that new hires get the right access before their first day, based on persona-based rules that consider role, location, and department. As soon as a new employee is created in the HRIS, Lumos triggers an automated provisioning workflow tailored to their needs.
For example, if a new engineer in San Francisco is starting next week, Lumos will automatically “Create email + assign to Jira group” five days before their start date. This means no waiting for IT tickets, no confusion about entitlements, and no delays in productivity. Birthright apps are assigned by default, and any additional requestable apps are visible in the AppStore from day one.
Automating the Mover Phase: Role Changes and Access Adjustments
As employees evolve within the organization, so should their access. Lumos continuously syncs with your HRIS to detect when someone changes departments, roles, or locations – and automatically recalibrates access accordingly.
If a marketing team member transitions into product management, Lumos revokes their old app entitlements and assigns new ones based on predefined policies. This automation eliminates the risk of permission creep, ensures least privilege, and removes IT from the middle of every team change.
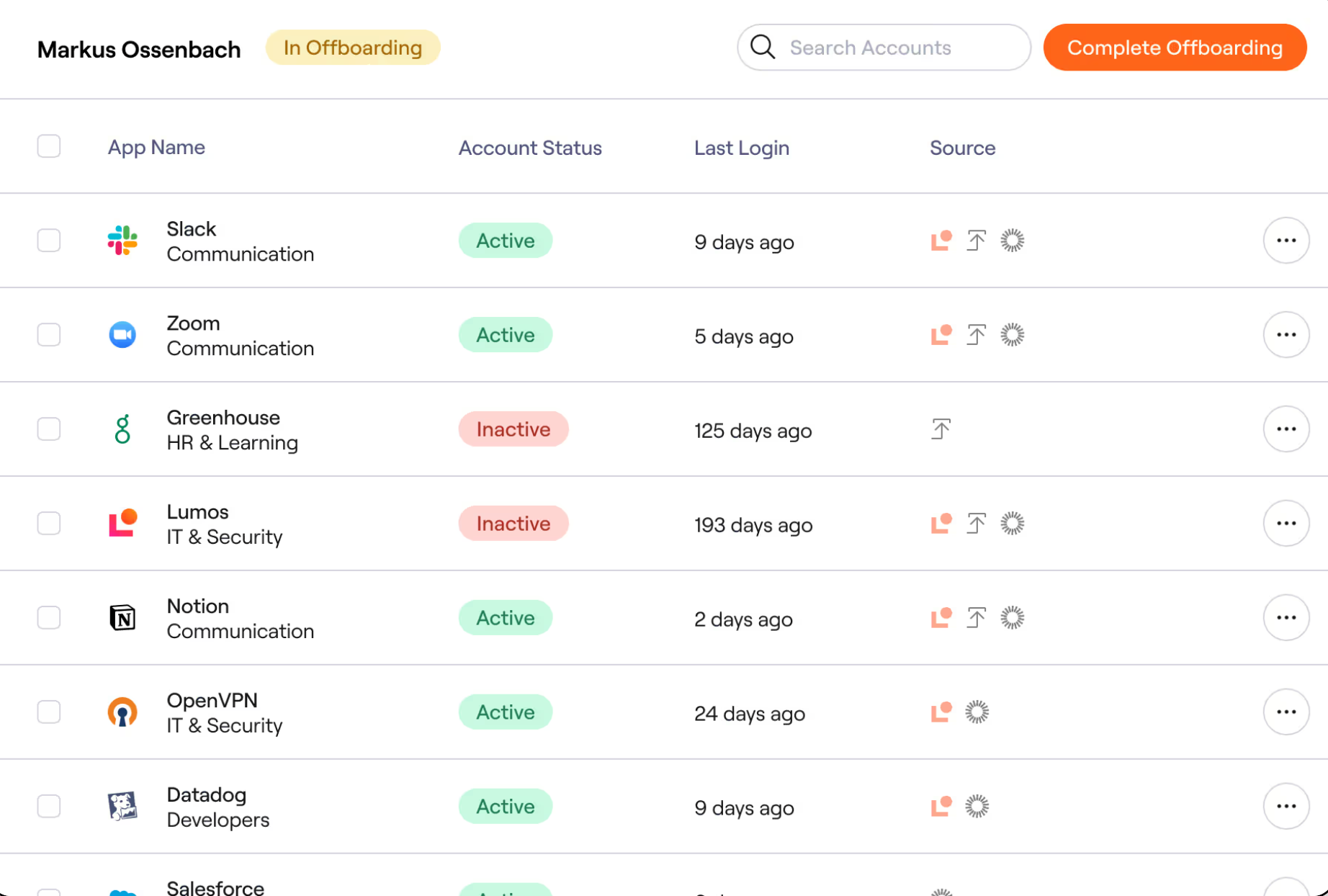
Automating the Leaver Phase: Fast, Secure Offboarding
Offboarding is a race against risk. Lumos starts the offboarding process the moment a termination event is registered in your HRIS. Access is set to auto-expire based on the employee’s last working day, with workflows that deprovision accounts across IdPs, SaaS apps, on-prem systems, and cloud infrastructure in a single policy-driven action.
App owners are notified automatically to take action, and IT teams have full visibility into task completion: ensuring nothing is missed and every account is closed. The result? Fewer orphaned accounts, cleaner audit trails, and dramatically reduced security risk.
With Lumos, JML becomes a high-impact, low-touch process that scales with your business.
Key Capabilities in a Modern JML Automation Platform
A mature JML automation platform must support complex environments, enforce least privilege, and empower teams across IT, security, and HR. Lumos delivers on all fronts, offering a comprehensive suite of capabilities designed to meet the demands of today’s hybrid enterprises. Here are some key capabilities for a JML automation platform:
- Integration Across Cloud, On-Prem, and Hybrid Environments
- Entitlement-Level Access Visibility
- Policy-Based Access Controls and Role Definitions (RBAC/ABAC)
- No-Code or Low-Code Automation Options
- Support for IAM and Governance Tools
Integration Across Cloud, On-Prem, and Hybrid Environments
Lumos connects to over 300+ applications out of the box, enabling centralized identity orchestration across SaaS, on-prem, and hybrid infrastructures. From collaboration tools like Slack and Zoom to developer environments like AWS, GitHub, and GCP, Lumos ensures access is governed and automated everywhere your teams operate.
Even better, Lumos leverages AI-powered integration tools to build new connectors in hours, not weeks. This means you can rapidly onboard new tools and enforce JML policies across your entire stack without waiting on custom development or third-party support.
Entitlement-Level Access Visibility
Broad access visibility isn’t enough; Lumos gives you entitlement-level granularity. This means you can see exactly which permissions a user has within each app, helping you identify overprovisioned accounts, unnecessary privileges, and misaligned roles.
With this granular insight, IT and security teams can confidently enforce least privilege, reduce attack surfaces, and build secure access policies that reflect real user needs – not just department-level assumptions.
Policy-Based Access Controls and Role Definitions (RBAC/ABAC)
Lumos supports both Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC) to help organizations automate access decisions dynamically. You can define policies based on job title, department, location, or any custom attribute. This ensures consistent, rules-based access enforcement throughout the user lifecycle.
To take it further, Albus, Lumos’ AI identity agent, analyzes historical access data and recommends optimized role definitions – accelerating RBAC/ABAC creation and reducing manual guesswork.
No-Code or Low-Code Automation Options
Whether you’re a seasoned admin or a business stakeholder, Lumos makes identity lifecycle automation accessible. With prebuilt workflows, easy-to-use policy builders, and self-service capabilities embedded in Slack and Microsoft Teams, teams can onboard faster, request access directly, and manage approvals without involving IT every time.
This no-code or low-code flexibility empowers functional teams to take ownership while still maintaining IT oversight and governance controls.
Support for IAM and Governance Tools
Lumos integrates seamlessly with your existing identity, HRIS and governance stack; including Okta, Microsoft Entra ID (Azure AD), Workday, BambooHR, and leading ITSM tools like Jira and ServiceNow. This ensures identity lifecycle workflows align with your current processes, enabling quick deployment and cross-functional adoption without disrupting operations.
Lumos is purpose-built to handle JML automation at scale: securely, flexibly, and intelligently. Whether you're a growing startup or a global enterprise, these capabilities ensure your identity workflows evolve with your business.
Why Now Is the Time to Automate Your JML Process
The way we manage identity has fundamentally changed. In a hybrid, cloud-first world, the traditional approach to onboarding, offboarding, and role changes – built on tickets, spreadsheets, and manual follow-ups – no longer scales. The risks are too high, the workloads too heavy, and the pace of change too fast. Organizations need a better way to manage the JML lifecycle; one that is secure, automated, and built for the realities of today’s workplace.
Lumos makes that vision real. As the Autonomous Identity Platform, Lumos eliminates the friction and risk of manual JML workflows, automating provisioning, deprovisioning, and access calibration across more than 300 apps. It delivers real-time visibility into who has access to what, applies least privilege by default, and ensures compliance through audit-ready logs and AI-powered insights.
But that transformation doesn’t have to happen all at once.
Taking the First Step: Start Small, Think Big
You don’t need to automate everything overnight. Start with a single department, say engineering or sales, and configure onboarding workflows with persona-based access bundles. Use Lumos to automate day-one provisioning, and test access removal for leavers based on real-time HRIS signals. Once you’ve proven success and gathered feedback, expand to additional teams, tools, and regions.
This crawl-walk-run approach lets you roll out with confidence, gain stakeholder buy-in, and continuously improve over time.
Use AI and Automation to Empower, Not Replace
JML automation isn’t about replacing people – it’s about amplifying your IT and security teams. Lumos takes the repetitive, error-prone tasks off their plates so they can focus on higher-value initiatives: security architecture, strategic vendor consolidation, or enabling new business units.
With Albus, teams get real-time insights on usage trends, policy gaps, and RBAC/ABAC opportunities. It’s not about handing off control; it’s about making smarter decisions, faster.
Make JML a Foundation of Your Security Strategy
Identity is no longer just an IT concern – it’s your new security perimeter. Every app, device, and employee interaction hinges on access. That’s why automating the JML lifecycle isn’t just a tactical win; it’s a strategic shift.
Lumos helps you secure access at scale, on autopilot. From day-one provisioning to final deprovisioning, from role-based adjustments to compliance-ready documentation, Lumos builds trust, efficiency, and resilience into every identity transition.
Ready to modernize your JML strategy? Book a demo with Lumos today and see how you can turn access into an advantage.
Keep Reading
Try Lumos Today
Book a 1:1 demo with us and enable your IT and Security teams to achieve more.





