User Access Review Automation: How to Automate User Access Reviews for Enhanced Security and Compliance
Efficiently automating user access reviews is essential for security. Learn how UAR automation streamlines processes, saves time, and boosts compliance efforts.


Automating user access reviews transforms a time-consuming compliance exercise into a continuous, risk-focused control that enhances security posture and audit readiness. By eliminating spreadsheets and manual email chains, organizations gain real-time visibility into entitlements, enforce least-privilege policies, and accelerate onboarding and offboarding.
In this guide, you will discover:
- What user access review automation entails and its importance
- Core benefits across security, compliance, efficiency, and cost savings
- Step-by-step mechanics of automated reviews and remediation workflows
- Critical software features—from connectors to AI-driven risk scoring
- Best practices, common use cases, and solution selection criteria
- Integration strategies with Identity Governance and Administration (IGA)
What Is User Access Review Automation and Why Is It Important?
User access review automation is the continuous, software-driven certification of user permissions across systems, replacing manual audits with dynamic campaigns that identify and remediate risky entitlements. This automation reduces human error, enforces least-privilege at scale, and maintains audit-ready records for compliance mandates.
For security teams, automated reviews enhance visibility into privilege creep and enable proactive risk mitigation, laying the groundwork for stronger identity governance.
What Is a User Access Review and How Does It Work?
A user access review is a periodic evaluation of individual entitlements to confirm that each user’s permissions align with current roles and responsibilities. It typically involves collecting access data, matching it against role definitions, and soliciting manager or system owner approvals.
Key steps in a manual access review include:
- Data Extraction: Exporting entitlement lists from applications
- Identity Mapping: Correlating user accounts with organizational roles
- Certification Campaign: Sending review requests to stakeholders
- Remediation: Revoking or modifying permissions based on feedback
- Audit Logging: Documenting approvals for compliance reports
This sequential process ensures that outdated or excessive privileges are removed, but it often suffers from long cycle times and error-prone communication.
What Are the Challenges of Manual User Access Reviews?
Manual user access reviews are a critical part of maintaining security and compliance, but they are often inefficient, error-prone, and difficult to scale. For IT and security leaders managing increasingly complex environments, relying on spreadsheets, email threads, and manual tracking creates unnecessary risk and operational drag. Here’s a closer look at the key challenges:
- Review Planning
- Access Verification
- Remediation
Review Planning
One of the biggest hurdles with manual access reviews is planning. Coordinating reviews across multiple departments and stakeholders often leads to delays and miscommunication. Reviewers may miss deadlines, misunderstand their responsibilities, or lack the context needed to make informed decisions.
This lack of alignment can stall compliance audits and leave security gaps unaddressed.
Access Verification
Verifying user access manually is not only tedious but also highly susceptible to errors and oversights. Reviewers are often forced to sift through massive spreadsheets or outdated lists, making it easy to overlook inappropriate access or fail to flag outdated permissions.
These gaps can leave sensitive data exposed, increasing the organization’s risk of insider threats or external breaches.
Remediation
Even after access issues are identified, remediation is often slow and inconsistent in manual processes. Without automated workflows, deprovisioning excess or unnecessary access typically involves opening tickets, coordinating across teams, and manually updating systems.
This lag creates audit gaps and compliance risks, as users may retain inappropriate permissions long after they should have been removed.
How Does Automation Improve User Access Reviews?
Automation platforms ingest access data, correlate identities in real time, and launch certification campaigns with built-in workflows and risk scoring. This automation reduces manual tasks, enforces policy consistently, and generates audit-ready reports.
Key improvements include:
- Continuous Monitoring: Automated polling of systems for entitlement changes
- Risk-Based Prioritization: Highlighting high-risk permissions first
- Configurable Workflows: Routing approvals to the right stakeholders automatically
- Audit Trail Generation: Immutable logs of every certification decision
This shift to automated processes accelerates compliance cycles and reinforces security by ensuring timely detection and remediation of anomalous access.
What Are the Key Benefits of Automating User Access Reviews?
Manual user access reviews are slow, error-prone, and challenging to scale, especially as organizations grow and adopt more cloud and SaaS platforms. Automating these reviews transforms the process from a reactive, labor-intensive task into a proactive, efficient, and reliable security control.
Below are the key benefits IT and security leaders can expect by embracing automation.
- Enhance Security and Reduce Risk
- Ensure Compliance with Regulations
- Increase Operational Efficiency and Cut Costs
- Improve Onboarding and Offboarding Processes
- Provide Better Visibility and Control
Enhance Security and Reduce Risk
Automation enforces least-privilege through continuous entitlement certification, preventing privilege creep and detecting abnormal access patterns.
This reduces the risk of insider threats, data breaches, and privilege creep; where users accumulate access rights they no longer need. By proactively flagging anomalies and providing clear remediation workflows, automation ensures that users only have access to the resources they need, and nothing more.
Ensure Compliance with Regulations
Automated user access review solutions generate audit-ready documentation that maps every review decision to regulatory requirements like GDPR, HIPAA, SOX, ISO 27001, and PCI DSS. Built-in compliance templates and regulation-specific checklists expedite certification campaigns.
Key compliance features include:
- Regulation-aligned review questionnaires
- Detailed time-stamped approval logs
- Standardized reporting for external audits
These capabilities promote consistent enforcement of internal policies and external mandates without manual report compilation.
Increase Operational Efficiency and Cut Costs
Manual access reviews consume significant time and resources. Automation eliminates repetitive, manual tasks, allowing IT and security teams to focus on strategic initiatives rather than chasing approvals or updating spreadsheets. Error reduction from software-controlled processes further minimizes rework and remediation overhead.
Primary efficiency gains:
- Time Savings: Instant data collection and campaign launch
- Error Reduction: Automated checks eliminate transcription mistakes
- Resource Optimization: Teams spend less time on routine audits
These improvements translate directly into cost savings on labor and compliance overhead.
Improve Onboarding and Offboarding Processes
Automated provisioning and deprovisioning integrate review campaigns with HRIS and identity providers to ensure new hires receive correct permissions and departing employees lose access immediately.
Onboarding and offboarding enhancements:
- Faster Provisioning: Preconfigured role assignments activated on hire
- Rapid Revocation: Automated deprovisioning triggers upon termination
- Audit Visibility: Real-time dashboards track onboarding status
Effective automation shortens ramp-up time for new employees and eliminates orphaned accounts.
Provide Better Visibility and Control
Dashboards consolidate access data across cloud platforms, on-prem applications, and data repositories, enabling stakeholders to monitor certification progress, review completion rates, and outstanding exceptions at a glance.
Visibility features:
- Real-Time Monitoring of campaign status and risk metrics
- Customizable Dashboards for executive and operational views
- Automated Notifications for overdue reviews
These capabilities empower organizations to maintain continuous oversight of user privileges and accelerate decision-making.
How Does User Access Review Automation Work?
Automated UAR follows a structured workflow: ingest, correlate, campaign, remediate, and report. Each phase leverages connectors and analytics to streamline certification and enforcement.
Automated user access review unfolds in five interlinked steps:
- Data Collection: Ingest entitlement data from HRIS, IDP, ITSM, and cloud services
- Identity Correlation: Map user accounts to roles and organizational units
- Campaign Execution: Launch certification campaigns with built-in questionnaires
- Remediation: Apply approved changes automatically via workflow engine
- Reporting: Generate audit-ready summaries and compliance dashboards
1. Data Collection: Consolidating Access Information
The process begins by aggregating entitlement and access data across your technology stack. This includes integrations with your HRIS (Human Resources Information System) for role and department data, IDPs (Identity Providers) for authentication details, ITSM platforms for service requests, and cloud and SaaS platforms for application-specific permissions.
By centralizing this information, automation tools create a single source of truth for all user access, eliminating the need for manual spreadsheets or siloed reports.
2. Identity Correlation: Mapping Access to Roles and Structures
Next, the system correlates user identities with roles, teams, and organizational hierarchies. This mapping ensures that every access right is tied to a specific user, role, or organizational unit. Accurate correlation is critical; it provides the context needed to evaluate whether current access levels are appropriate, excessive, or outdated.
3. Campaign Execution: Streamlined Certification Workflows
With data mapped and organized, automated platforms launch certification campaigns. These workflows notify managers, application owners, or compliance leads to review access for their teams. Built-in questionnaires and approval forms simplify the review process, guiding reviewers to make informed, consistent decisions without sifting through complex entitlement data manually.
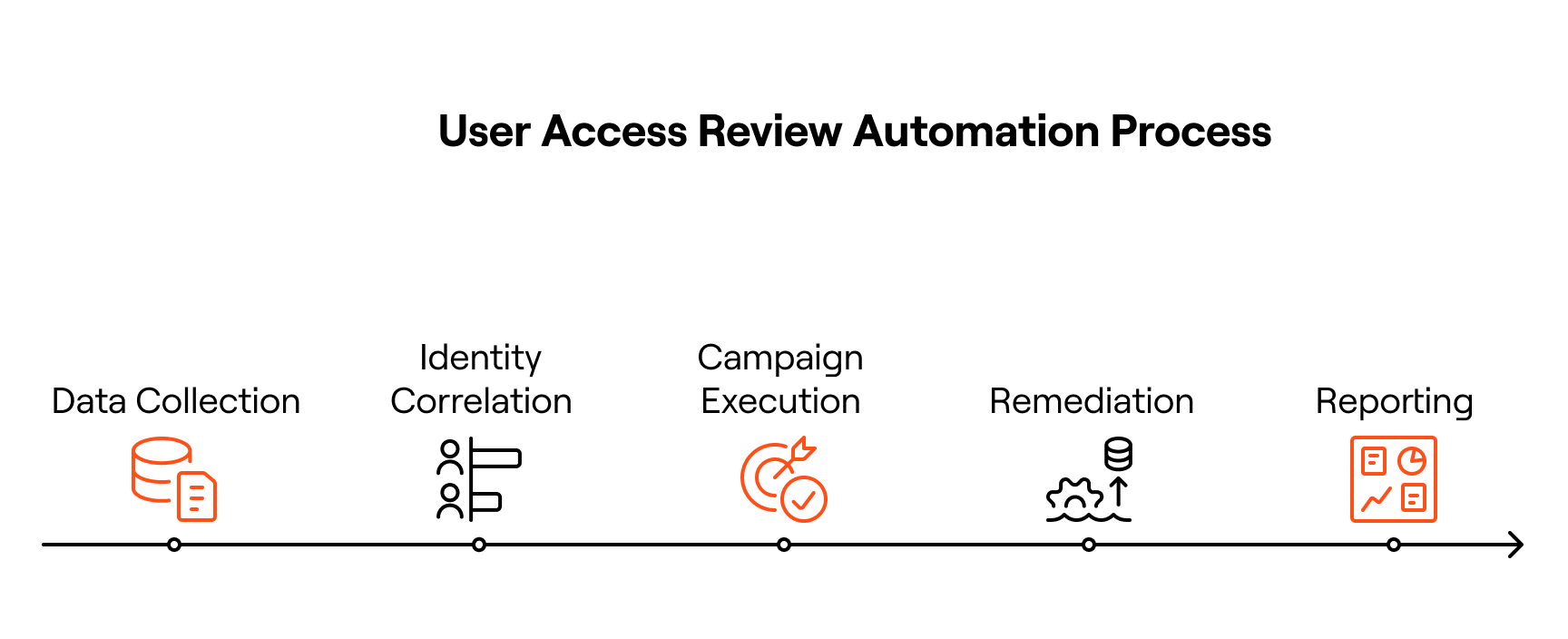
4. Remediation: Automated and Policy-Driven Changes
When a review identifies excessive or unnecessary access, automation enables policy-driven remediation. Instead of waiting for manual IT intervention, workflow engines execute approved changes: revoking, adjusting, or granting access instantly. This not only reduces human error but also accelerates response times, ensuring access is always aligned with organizational policy.
5. Reporting: Audit-Ready Documentation
Finally, automated platforms generate detailed, audit-ready reports and compliance dashboards. These records provide a complete trail of actions and approvals, simplifying regulatory audits and demonstrating adherence to internal controls and external requirements such as SOX, HIPAA, or ISO 27001.
What Are the Essential Features of User Access Review Automation Software?
Effective UAR automation software is designed to simplify complex processes, reduce manual workloads, and ensure compliance with regulatory standards.
By incorporating integrations, artificial intelligence, workflow automation, and policy-based governance, these platforms deliver greater accuracy, scalability, and security. Below, we break down the key features that IT and security leaders should look for in a modern UAR automation solution.
How Do Connectors and Integrations Support UAR Automation?
Connectors are the backbone of any automation platform. Modern UAR tools integrate seamlessly with identity providers (IDPs) like Okta or Azure AD, HRIS platforms such as Workday or BambooHR, and ITSM systems like ServiceNow or Jira.
By ingesting entitlement and activity data from these systems, the platform creates a comprehensive view of user identities, roles, and access levels. These integrations reduce manual data entry, eliminate inconsistencies, and ensure that access reviews reflect real-time information across cloud, on-premises, and hybrid environments.
For organizations operating in multi-cloud environments, these integrations are key to achieving centralized governance and consistent policy enforcement across all platforms.
What Role Do AI and Machine Learning Play in UAR Automation?
Artificial intelligence (AI) and machine learning (ML) are transforming UAR automation by providing intelligent insights and adaptive workflows. AI-driven platforms analyze historical usage patterns, entitlement data, and organizational structures to:
- Recommend role-based policies for more accurate reviews
- Detect anomalies and risky access patterns in real time
- Prioritize high-risk accounts for faster remediation
By learning from previous certifications and user behavior, AI enables continuous improvement in the accuracy and efficiency of access reviews. This not only saves time for IT teams but also strengthens the organization’s risk management and compliance posture.
How Do Workflow Automation and Delegation Improve Access Reviews?
Manual access reviews often stall due to bottlenecks in approvals and follow-ups. Workflow automation solves this by streamlining every step of the process. Key capabilities include:
- Automated review campaigns triggered by policy schedules
- Delegation capabilities that route reviews to the correct managers or app owners
- Approval workflows that escalate high-risk cases to senior stakeholders
These automated workflows ensure timely completion of campaigns and help organizations meet audit deadlines while reducing administrative burden. By eliminating manual tracking and email chains, IT teams can focus on strategic initiatives rather than routine follow-ups.
How Are Role-Based Access Control and Segregation of Duties Supported?
Effective UAR automation platforms also embed Role-Based Access Control (RBAC) and Segregation of Duties (SoD) principles into their frameworks. This ensures that users only have the minimum access required for their roles and that no single user has conflicting permissions that could lead to compliance violations or security risks.
For example, automated systems can:
- Identify conflicts between finance and approval roles
- Flag exceptions that violate internal controls or regulatory requirements
- Enforce least-privilege policies consistently across applications and environments
By integrating RBAC and SoD checks directly into the review process, organizations can proactively prevent security gaps and improve audit readiness.
What Are Best Practices for Implementing User Access Review Automation?
Successful automation initiatives combine policy clarity, continuous monitoring, and stakeholder engagement to achieve sustained governance.
How Should Policies Be Defined for Effective UAR Automation?
Clear, enforceable policies form the foundation of automation. Define role templates, risk thresholds, and review frequencies based on job functions and data sensitivity.
Key policy elements:
- Role Definitions aligned with business processes
- Access Certification Frequency (quarterly, monthly, continuous)
- Risk Classification for high-privilege entitlements
Well-structured policies ensure that automation enforces consistent controls organization-wide.
How Can Continuous Monitoring and Access Certification Be Achieved?
Shift from periodic audits to real-time review campaigns that trigger on entitlement changes, new hires, or policy updates.
Continuous monitoring methods:
- Event-Driven Reviews initiated by identity lifecycle events
- Adaptive Campaigns that adjust scope based on risk scores
- Ongoing Audit Trails for uninterrupted compliance evidence
This approach embeds certification into daily operations, reducing audit surprises.
How Should Stakeholders Be Involved in the Automation Process?
Engage application owners, managers, and compliance teams early to define review scopes, approval hierarchies, and exception handling.
Stakeholder engagement practices:
- Kick-Off Workshops to align on roles and responsibilities
- Training Sessions on review workflows and dashboards
- Periodic Governance Forums to refine policies and SLAs
Active collaboration fosters accountability and smooths the path for automation adoption.
What Are Common Use Cases for User Access Review Automation?
Automation extends across multiple scenarios—from regulatory audits to specialized privilege controls and third-party access management.
How Is UAR Automation Used for Onboarding and Offboarding?
Automated campaigns tie directly into identity lifecycle events from HR systems, ensuring that new employees receive correct roles and departing users lose access immediately.
Onboarding and offboarding workflow:
- HR Triggered Campaigns for new hires and terminations
- Role Assignment Automation based on job profiles
- Access Revocation linked to termination effective dates
These use cases eliminate orphan accounts and streamline user transitions.
How Does Automation Support Role-Based Access Control Management?
Role-based review campaigns verify that each role continues to map to appropriate entitlements, promoting consistent access models.
RBAC certification tasks:
- Role Entitlement Audits to confirm role integrity
- Role Change Notifications when policies or organizational structures shift
- Role Optimization Reports suggesting role consolidations
This ensures that roles remain aligned with evolving business needs.
How Does UAR Automation Detect and Prevent Privilege Escalation?
By continuously monitoring privilege assignments and comparing them against risk policies, automation platforms catch unauthorized privilege grants in near real time.
Privilege escalation controls:
- Real-Time Event Monitoring for new administrative privileges
- Risk Alerts for sudden entitlement spikes
- Automated Rollbacks for unauthorized privilege assignments
Proactive detection reduces the window of exposure for elevated access.
How Is Third-Party and Vendor Access Managed Through Automation?
External user reviews integrate vendor directories and partner portals into certification campaigns, ensuring that third-party accounts adhere to access policies.
Vendor access management:
- Integrated Vendor Connectors for partner identity systems
- Periodic Certification of external entitlements
- Time-Bound Access enforcement with automatic expiry
This use case strengthens oversight of non-employee access across applications.
How Do You Choose the Right User Access Review Automation Solution?
As organizations scale and regulatory pressures grow, UAR automation software has become critical for IT and security leaders. These platforms simplify complex access reviews, enforce least-privilege policies, and ensure compliance; all while reducing operational overhead. Below, we explore the essential features to look for, how tools compare, and the potential return on investment (ROI).
What Features Should You Prioritize When Selecting UAR Software?
When evaluating UAR automation tools, focus on platforms that deliver integration, intelligence, and usability:
- Seamless Integrations: The software should connect easily with your identity providers (e.g., Okta, Azure AD), HR systems (e.g., Workday, BambooHR), ITSM platforms (e.g., ServiceNow), and SaaS apps to centralize entitlement and usage data.
- AI-Powered Insights: Look for tools that leverage AI to recommend policy adjustments, flag anomalies, and streamline access reviews.
- Configurable Workflows: Automated workflows for certifications, approvals, and remediation are key for reducing manual effort and human error.
- Audit-Ready Reporting: Compliance dashboards and downloadable audit trails simplify preparation for SOX, HIPAA, or ISO audits.
- User-Friendly Experience: Platforms with intuitive interfaces empower managers and reviewers to complete certifications quickly and accurately, reducing friction.
These core features ensure automation delivers both security and efficiency, while remaining adaptable to your organization’s needs.
How Do Different UAR Automation Tools Compare?
Not all automation tools are created equal. Legacy IGA platforms often provide robust compliance features but lack flexibility, resulting in longer deployments and steep learning curves. On the other hand, next-generation UAR solutions prioritize speed, scalability, and ease of use, offering:
- Agent-driven intelligence for contextual recommendations.
- Faster implementation timelines; often within weeks instead of months.
- Modern integrations with cloud and hybrid environments.
When comparing vendors, consider your environment size, complexity, and regulatory requirements. Organizations with hybrid infrastructures or high compliance demands will benefit most from platforms that combine deep integration capabilities with real-time analytics and policy-based automation.
What Is the Return on Investment (ROI) for UAR Automation?
Investing in UAR automation delivers measurable benefits that go beyond compliance:
- Operational Efficiency: Automating campaigns and remediation eliminates manual tasks, saving hundreds of staff hours annually.
- Reduced Risk Exposure: Continuous monitoring and AI-driven anomaly detection help close security gaps and minimize the risk of insider threats or credential misuse.
- Compliance Cost Savings: Automation reduces the time and resources needed for audits, minimizing penalties and streamlining certification evidence collection.
- Scalability: As your organization grows, automation ensures that access reviews remain accurate and timely without proportionally increasing staff workload.
For many enterprises, the ROI is clear within the first year, driven by time savings, reduced risk exposure, and improved audit readiness.
Driving the Future of User Access Review Automation with Lumos
Manual User Access Reviews aren’t just inefficient; they’re a risk. As organizations scale their SaaS footprint and adopt hybrid work models, visibility into who has access to what becomes harder to maintain and more critical to get right. Automating UARs is essential for enforcing least privilege, passing audits, and reducing security exposure at scale.
Lumos is purpose-built to automate and modernize access reviews across the entire identity lifecycle. With deep integrations into your HRIS, Identity Provider, SaaS apps, and ITSM tools, Lumos centralizes the entire review process: automating campaign creation, reviewer assignments, escalation workflows, and evidence collection.
- Granular, entitlement-level visibility lets reviewers see not just what app a user has access to, but their exact permissions and how they got them.
- Time-bound and policy-driven reviews ensure access is only granted when necessary, and removed when no longer needed.
- Albus, Lumos’ AI identity agent, flags access anomalies, recommends removals, and surfaces misaligned entitlements – so reviewers can take smarter action, faster.
For IT, this means fewer tickets and better audit readiness. For security and compliance teams, it means automated proof of least privilege, clear audit trails, and reduced review fatigue. And for the business, it means cleaner access, faster certification cycles, and a lighter burden on stakeholders.
Traditional access reviews are slow, error-prone, and disconnected. Lumos changes that by turning UARs into a proactive, intelligent, and scalable workflow that keeps your organization secure; without slowing it down.
Ready to simplify compliance and scale access governance? Book a demo with Lumos today and see how we automate user access reviews with precision and confidence.
Try Lumos Today
Book a 1:1 demo with us and enable your IT and Security teams to achieve more.