Traditional IGA Doesn't Scale. Agents Do.
See all your identities, understand what's actually risky, and fix at scale.
All in one platform.








Close the Loop and Bring Your Identity Risk Under Control
Lumos Identity Intelligence combines continuous visibility, AI-powered risk analysis, and Identity Security agents to fix what you find, all in one place. Stop reacting to risk and start remediating it.
See everything
See everything Complete visibility across every identity - human, NHI, and AI agent - across all your apps and directories, normalized into a single view.
Understand what matters
Continuous, correlated analysis that ranks risk by actual exposure - not noise. Know what's anomalous, what's overprovisioned, and what needs to move first.
Act at scale
Identity Security Agents that investigate findings, execute remediation, and improve through feedback - closing the loop from insight to action without a human in every step.
Key Features

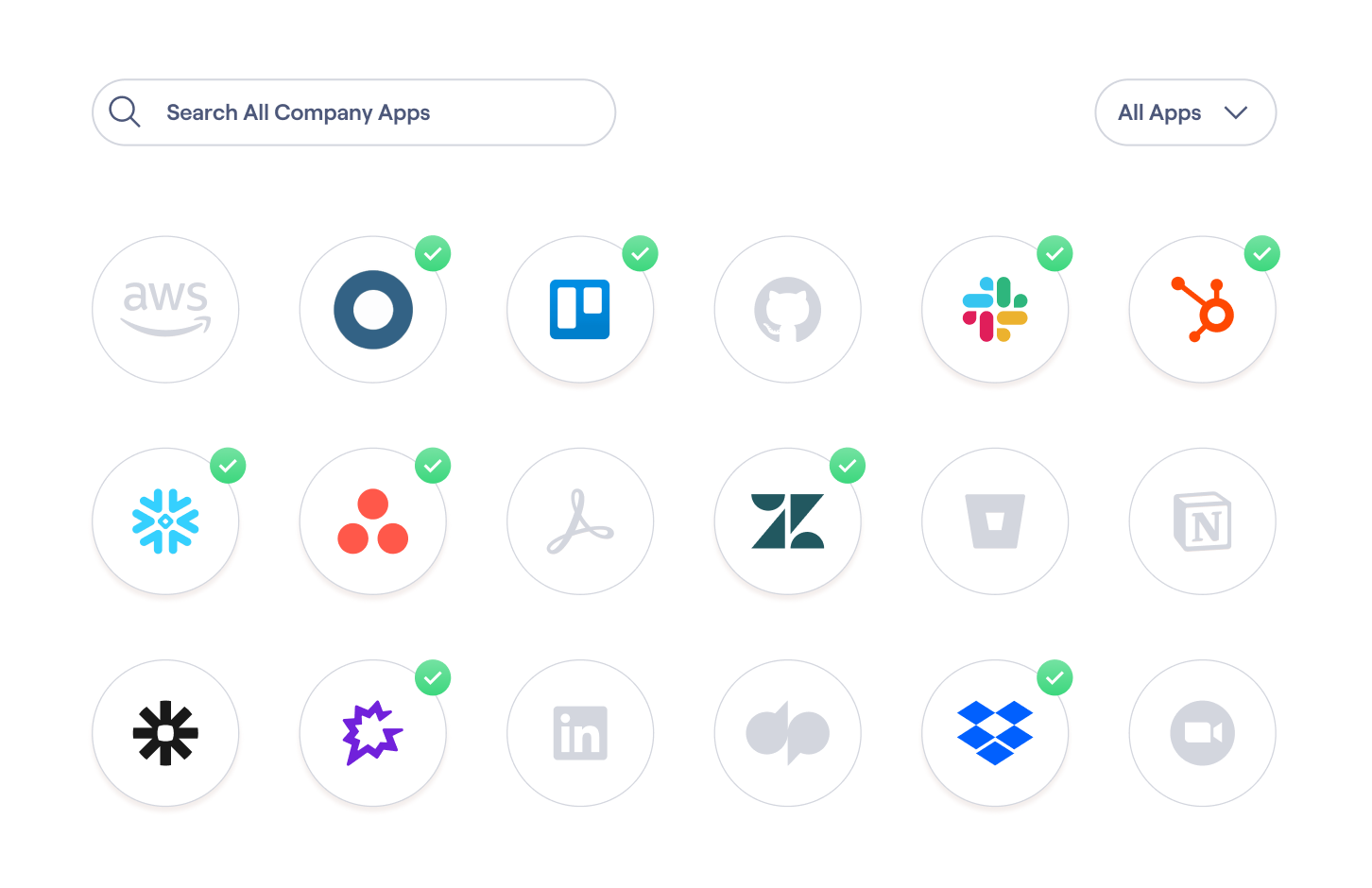
See every identity across your entire environment
Lumos builds a unified access graph that keeps up with the rapidly expanding scale across every connected app, directory, and identity type - human employees, service accounts, API keys, and AI agents. Understand granular entitlements with real usage context, so you know exactly who - or what - has access to which resources and what that access actually means.
Get AI-ranked findings with the reasoning behind them
Identity Security Agents continuously correlate HRIS, IdP, app, and usage signals to flag anomalous access, privilege spikes, orphaned accounts, and SoD conflicts, scored and explained in plain language. No manual investigation required to get to the first finding.


Put agents to work closing the loop
Identity Security Agents act on what intelligence surfaces: investigating findings, coordinating remediation, and executing fixes without waiting on a human to pick up the ticket. Write instructions in plain language, review output, give feedback, and your agents are calibrated to your environment in a single session. Not weeks of configuration.
Outcomes You Can Measure












Additional Resources
Frequently Asked Questions
Identity Security Posture focuses on continuous monitoring and risk prioritization. Identity Intelligence adds the full closed loop - security agents that act on what's surfaced, so findings don't just accumulate in a dashboard.
Not necessarily. Lumos can extend your existing stack with an AI agent layer, or serve as your end-to-end identity platform. The closed-loop story works both ways.
Human identities, non-human identities (service accounts, API keys, workload identities), and AI agents - with entitlement-level context across all of them.
You assign agents to specific jobs using natural-language instructions. They surface findings for your review, learn from your feedback, and calibrate to your environment's exceptions and priorities in a single session, not weeks of configuration.
Identity Intelligence is available now. Security Agents are available via waitlist.
Try Lumos Today
Book a 1:1 demo with us and enable your IT and Security teams to achieve more.



